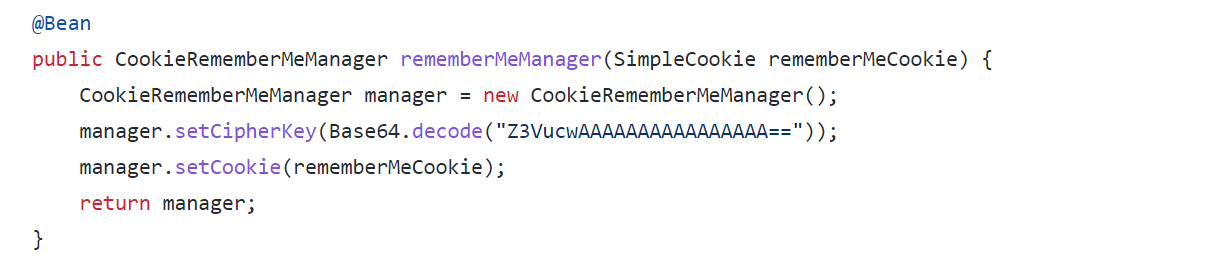
In http://material-admin/material-manage/src/main/java/cn/enilu/material/admin/config/web/ShiroConfig.java we can find a fixed key and uses this key to encrypt the rememberMe parameter in the cookie. It will cause deserialization vulnerability
I set up a a local environment for attacks.
I found that the source code contains commons-collections-3.2.2.jar and commons-beanutils-1.9.4.jar dependency, which is actually a dependency included in shiro.
Using this dependency, it is possible to generate a deserialized payload and then encrypt the payload using the key obtained by blasting. write this payload after the rememberMe field and attack it. Successful RCE.

In
http://material-admin/material-manage/src/main/java/cn/enilu/material/admin/config/web/ShiroConfig.javawe can find a fixed key and uses this key to encrypt the rememberMe parameter in the cookie. It will cause deserialization vulnerabilityI set up a a local environment for attacks.
I found that the source code contains commons-collections-3.2.2.jar and commons-beanutils-1.9.4.jar dependency, which is actually a dependency included in shiro.
Using this dependency, it is possible to generate a deserialized payload and then encrypt the payload using the key obtained by blasting. write this payload after the rememberMe field and attack it. Successful RCE.